It might be just me watching too many criminals with the investigative journalists as leading characters. Perhaps I felt that otherwise it would not work. Anyway, I spent a large chunk of the last year inside a Facebook group responsible for hacking other groups and accounts.
With my own eyes, I witnessed the permanent removal of numerous Facebook pages and saw popular groups being hacked.
They often belonged to my friends' friends. I didn't warn you. I couldn't do it, I am very sorry.
The members of a Polish Facebook group called "Putin's Bastards" (so-called бп), which was a group engaged in Internet "trolling" . They probably already knew that there was an infiltrator among them.
So at one point, I decided that I had seen enough of their content.
I didn't pass another "inner test", and decided to end my private investigation.
I did it all in order to work out their ways and develop a suitable defense plan that I can share with you. Unfortunately, before I managed to take decent screenshots of more serious actions of the group (a day after a popular Polish newspaper called “Gazeta Wyborcza” published an article about the group), the group admins created private chats to catch the infiltrator.
Instead of waiting, I could’ve watched them as they went. Unfortunately, I didn't think about it back then - I was busy analysing the events and the group disappeared in one day, breaking up into several smaller groups (the abovementioned private chats).
Why do people hack other people's groups?
Before the described above happened, I was really fed up with what I was experiencing after a few months of being a member of that group. The content wasn’t religiously inappropriate, racist or hateful. It was however wrong on all kinds of levels - I felt deeply disgusted with the horrible memes posted by the members.
I couldn't explain to myself why or how anyone could derive any pleasure from such activities.
Taking over a vegan group to write about meat, a weight loss group to call names those who share their progress, or a group for moms. Endlessly entertaining, isn’t it?
Especially when the new administrator is one of the bullies and the former administrator ... well, they didn't even realize that they are no longer the administrator.
I was speechless seeing so much hatred resulting purely from boredom and the lack of anything better to do.
Seriously, they didn't even do it for money as some online trolls have done before.
The group members posted tons of stupid content (including the memed) but sometimes they would openly ask each other about harming new people:
Do you know any losers who have nice groups cause I am stuck at home doin’ nothin’ today?
(* I will explain the meaning of the quote in the following paragraphs)
Who hacks Facebook groups?
After I read all this rubbish, one more conclusion came to my mind. Of course, it was impossible to verify the members of the group. Everyone used false names, and when it turned out that someone allowed someone logged in to a real account to enter the group, it ended up with a permanent ban (I didn't know that before the infiltration - so I assume my personal data was super helpful here, too).
Due to false identities, it was impossible to figure out who the Putin's Bastards really were or what they did. However, this could be deduced from their behavior and their language. The vast majority of them turned out to be middle school or high school students who were looking for ways to kill boredom and build a sense of belonging. How were such young people able to carry out serious hack attacks?
What does the attack look like?
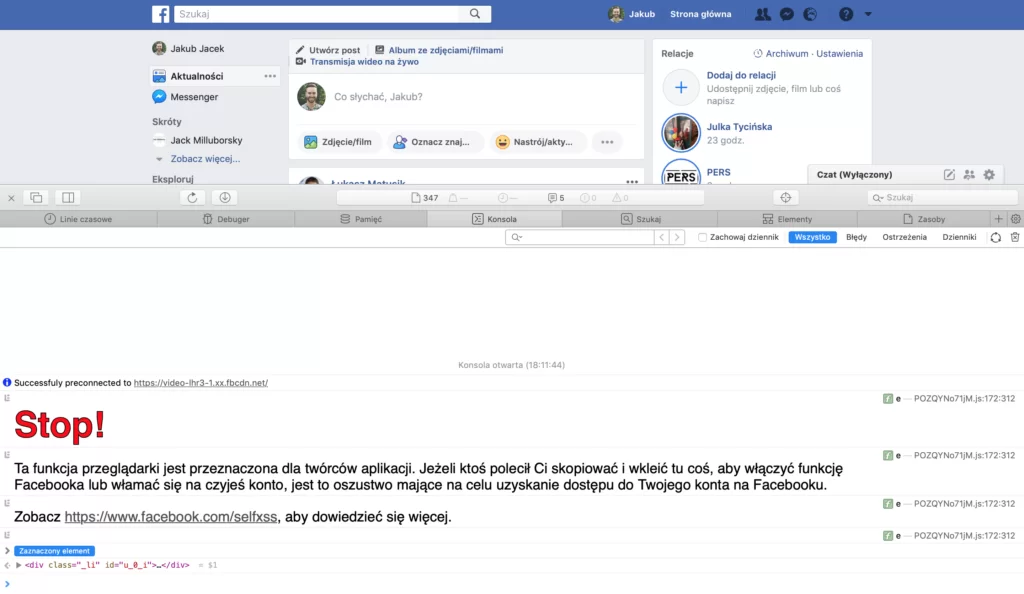
Basically, to hack a group or a Facebook page is not that complicated at all. And with the right piece of code, even a newbie could do it.
The mechanism itself is quite simple, and we sometimes let them hack our pages with our curiosity and recklessness.
The same pattern of infecting user's devices with a prepared virus is known for years. Professionals call it social engineering.
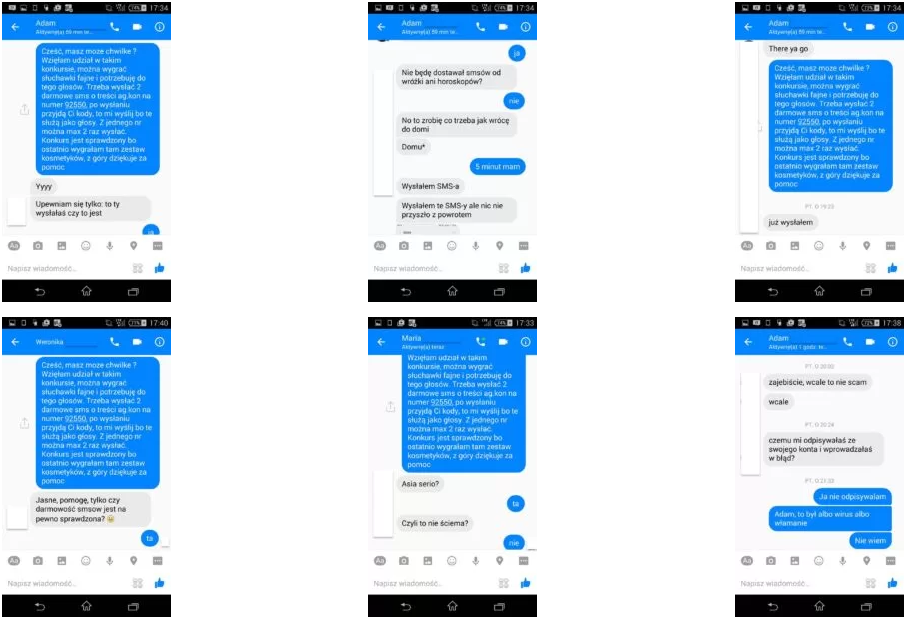
Once widespread in emails, today adapted to the Facebook reality - based on people's curiosity, it collects its toll every day, especially in conjunction with automated scripts written by the Internet "thieves", with whom some of you might have had an encounter.
The mechanism is as simple as effective - after clicking on the link included in a very tempting message, we call the code that does all the work for us - it is able to change passwords, ownership of your Facebook group, to manage rolls on Facebook pages and advertising accounts, check your card details, photos or even message content.
Sometimes it may be a good old conversation leading to the photos of naked breasts being sent out, or a simple photo we are supposedly tagged in.
We used to be pursued by hackers to paste such codes ourselves, but nowadays clicking a link does the job for us.
Very simple and convenient, right?
How to recognize the "attack" and how to successfully prevent it?
Not long after I left the group, I received numerous suspicious friend requests. They looked like this:
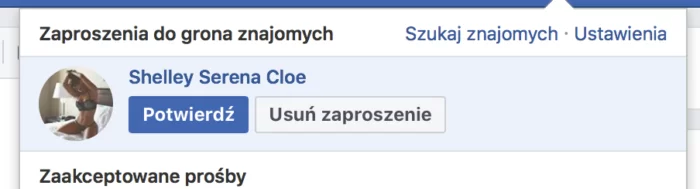
It's nothing more than taking the least resistance path and trying to get me into a conversation that ends with sending me a virus.
Of course, nothing will happen if you accept an invitation from such a stranger. You will also be fine when you talk to them. The most important thing is to stay alert and:
- Do not click on suspicious links. How to recognize them? Basically, any link sent by a stranger should be treated as such. If someone really wants us to see what is happening on a given page, we can always ask for a screenshot via messenger, much safer than following the unknown link. If they refuse - it should be an obvious sign for you.
- Do not send them any photos. The photos you take on a daily basis with your smartphone have geotags enabled by default, which surprisingly accurately indicate your geographic location. You never know what they might use it for later.
- Do not send any SMS. Even if you're asked allegedly by your friend. While a few years ago the way automated scripts conducted conversation was obviously limited and after a short discussion (usually receiving answers in broken English)it was obvious you were talking to a bot, the modern bots not only make a lot of sense but can also use fluent and even fancy language.
The guide listed above isn’t limited to Facebook only,
It also concerns suspicious links inside Facebook groups or comments under our posts.
Before you click on any link, read carefully three times to see if you are sure it leads to http://facebook.com instead of http: //faceboọk.com or to https://youtube.com instead of https://yuo.tube.com
These are just pre-made variations of popular website addresses, which after entering may look almost identical to the originals, but all actions (including the password entered on them) will be registered on the hacker's server and associated with your account and data.
This type of attack impersonating someone else or a trusted website, combined with the above-mentioned social engineering is usually extremely effective. Mainly because of our curiosity and carelessness.
After all, we are only human, and as they say - curiosity killed the cat.
To stay safe, we all should consider protecting our social media accounts with additional passwords, double verification, one-time SMS codes, and other tools reducing the chances of becoming a cyber victim.
Every week I write about the most important changes and news in the world of social media marketing. No spam, no chit-chat. The meat itself!


